Most of us use our email accounts without second thoughts about security. We choose a password that, we think, is secure and then forget about it entirely. Human beings have a habit of taking things for granted, and most of us assume that our account is safe and secure and will never be compromised.
After reading several reports of high-profile breaches in security that resulted in compromised email accounts, I decided to check out the tools that everyday email users can use to detect any unauthorized intrusions into their accounts. Gmail is my primary email provider. I have a standard Google account and a Google Apps account provided as an alumni service by my alma mater, Virginia Tech. So I decided to investigate the tools that Google provides to address this issue. In this blog post, I will document what I discovered.
So, what do you do if you suspect that your Gmail account has been compromised? The first thing you need to do is determine if your account has been accessed from a computer you do not normally use. In other words, it would be nice if your email provider could provide you with a list of IP addresses that have accessed your account. Turns out that Gmail does just that.
When you open your Gmail account, there is an entry called “last account activity” at the bottom of the webpage. Here is an image of this feature.
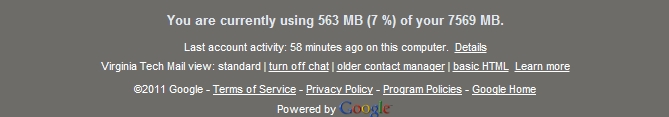 Last Account Activity
Last Account ActivityAs can be seen in the image above, there is a “Details” link at the end of the “last account activity” line. Clicking this link leads you to a pop-up screen with details of the IP addresses that last accessed your account. Here is a screen-shot of the window that I got when I clicked this link.
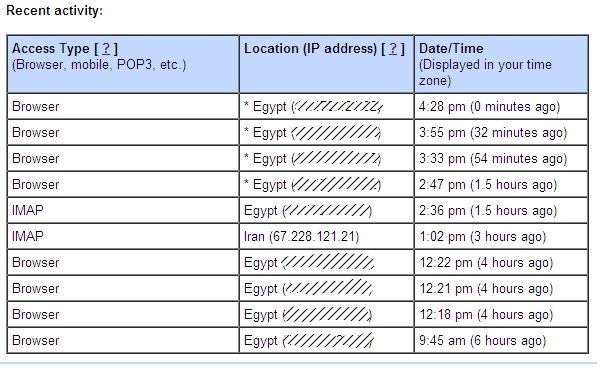 IP accesses
IP accessesThe hashed out IP addresses are mine. You will notice, however, that there is an IP address listed as originating in Iran. Since I am pretty sure I haven’t teleported to Iran recently, this raised a red flag. I had my few minutes of “oh my God, the Iranians are after me”, and then remembered my geek roots 😀
When in doubt about IP addresses, whois is your best friend. I did a whois on the IP address and it turns out that it belongs to Gist via SoftLayer Technologies Inc. Gist is a contact management software that I had previously subscribed to. So it turns out that the Ayatollahs are not out to get me after all 🙂 Though I am still having a hard time trying to imagine why Gist would have its servers, or some of its servers, in Iran. Oh well, there is no accounting for the decisions that international companies make.
So, to summarize, in order to determine whether or not your Gmail account has been compromised, you first need to identify the IP addresses that have accessed your account, and then do a whois on IP addresses that you are unfamiliar with. In most cases, those IP addresses will turn out to belong to websites that you have authorized to have access to your account, but it doesn’t hurt to be careful.
Anyway, this entire exercise brought up another question. What would I have done if my account had been compromised? I am not the type of person who uses the same password for all his accounts, but if I had been, a breach in security in any of my accounts could have compromised most of my online activity.
While I consider my online security regimen above average, I have become lapse in my security procedures in the last couple of months. I no longer regularly changed my passwords and some of my passwords contained dictionary words. So I decided to revive my security regimen.
There are two tools that can greatly improve your security procedure. They are KeePass and DropBox. I use KeePass to generate extremely strong passwords for all my accounts, at least I used to before I had my security lapse. I am now back to using KeePass to generate passwords. However, the passwords generated by KeePass are usually too difficult, for me its more like impossible, to remember. So how do I manage to access my email account if I cannot remember my password?
Simple, KeePass generates a password database file. All I have to do is put this password file in my DropBox folder and let DropBox do its magic. DropBox is a cloud-based storage service that automatically syncs files on all devices that have the software installed. This way I can always access my KeePass password database.
So my revived security measures include creating strong passwords using KeePass and using its expiry feature to make mandatory changes every few weeks, and then syncing the KeePass database to the cloud using DropBox to ensure that I always have access to my passwords. You should give this a try, it’s never a bad idea to implement good security practices.




2 Comments